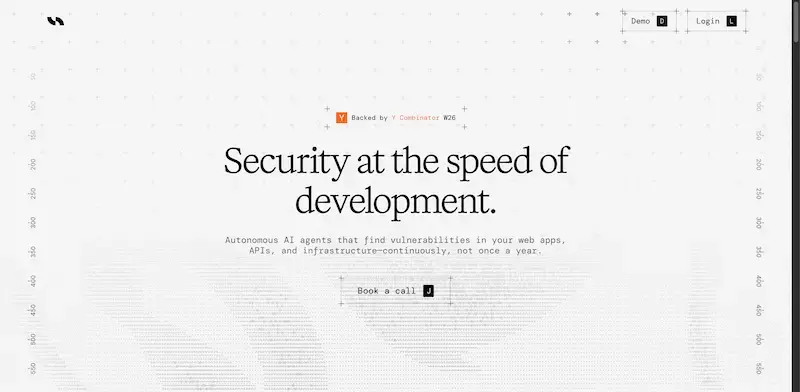
Hex Security
Autonomous security testing that finds vulnerabilities before attackers
Autonomous security testing that finds vulnerabilities before attackers
- Use Cases
- Not listed yet
- Pricing
- Custom
- Platforms
- Not listed yet
Overview
Hex Security deploys autonomous AI agents that run continuous penetration tests against web applications, APIs, and infrastructure to discover critical vulnerabilities before attackers exploit them. Built by YC W26 founders, the platform addresses the $10 trillion annual loss from preventable security flaws by replacing expensive, slow, once-yearly manual pentests with intelligent agents that work around the clock, chain exploits together, and deliver actionable findings with proof-of-concept demonstrations and remediation steps.
Continuous Autonomous Testing:
AI agents scan your systems 24/7 instead of annual assessments, identifying new vulnerabilities as your codebase evolves and catching security gaps that emerge between traditional penetration test cycles.
Details
Exploit Chain Discovery:
The platform doesn't just find isolated vulnerabilities; it intelligently chains multiple exploits to demonstrate real attack paths, revealing how attackers could escalate privileges or move laterally through your infrastructure.
Validated Proof-of-Concepts:
Every vulnerability report includes working demonstrations and reproduction steps verified by the AI agents, eliminating false positives and providing security teams with clear evidence and remediation priorities.
YC-Proven Track Record:
Already discovered critical vulnerabilities across dozens of prominent Y Combinator companies, including SQL injections exposing billions of records, authentication bypasses, and access control flaws that could enable full account takeovers.
Fraction of Traditional Costs:
Automates security assessments that typically require six-figure budgets and weeks of consultant time, making enterprise-grade penetration testing accessible to startups and scaling companies.
Who This Is For
Fast-Growing Tech Companies:
Startups and scale-ups shipping code daily who can't afford the delays of scheduling manual pentests or the risk of deploying vulnerabilities between annual security audits.
DevOps and Security Teams:
Engineering organizations responsible for maintaining secure infrastructure that need continuous validation that new deployments haven't introduced exploitable flaws without bottlenecking development velocity.
Compliance-Focused Enterprises:
Companies pursuing SOC 2, ISO 27001, or industry-specific certifications require regular penetration testing evidence but struggle with the cost and scheduling challenges of traditional security consultants.
Common Questions
How is this different from automated vulnerability scanners?
Traditional scanners only detect surface-level issues, such as known CVEs. Hex Security's AI agents reason like elite penetration testers, discovering complex logic flaws, chaining exploits, and testing business logic vulnerabilities that automated scanners miss entirely.
Won't continuous testing disrupt our production systems?
The AI agents are designed to test safely without causing service disruptions, much as professional penetration testers do. You maintain full control over testing scope, timing, and intensity through the platform's configuration settings.
What happens after the AI finds vulnerabilities?
You receive detailed reports with severity ratings, proof-of-concept demonstrations, affected code locations, and specific remediation guidance, enabling your development team to prioritize and fix issues immediately rather than waiting weeks for consultant-written PDFs.
How quickly can we start seeing results?
After a discovery call and scope definition, Hex Security can begin testing within days, with initial vulnerability findings typically delivered within the first week of continuous monitoring against your systems.
Alternatives
A shortlist of related products to compare before you leave the page.

Protect your users' data with automated security checks and easy fix suggestions tailored...
CheckYourVibe is a free security scanner designed to help app developers built with AI identify and fix critical security issues, ensuring the integri...
- Automated security scans that detect critical issues such as exposed API keys, missing HTTPS, and public admin panels without authentication, providing a comprehensive security audit in minutes.
- Plain English results and custom fix prompts that enable developers to quickly understand and resolve security flaws, even without extensive security expertise, and integrate seamlessly with AI tools like Cursor, Claude, and ChatGPT.
- Pro-level analysis that identifies injection vulnerabilities, security header issues, and authentication flaws, giving developers a deeper understanding of their app's security posture and enabling them to ship updates confidently.

Get Compliant, Fast — Powered by AI Automation
Delve is an AI-native compliance platform designed to help fast‑growing companies effortlessly meet rigorous standards like SOC 2, HIPAA, ISO 27001, G...
AI that handles security audits, so you don’t have to
Designed for modern startups and scaling teams, Comp replaces spreadsheets and manual checklists with a smart system that works in the background—keep...
Resources
Useful Links
Launched
Ideal for
Ownership
If this is your product, contact us and we can help transfer it to you.